Author: Roman Shneer
Viewers: 731
Last month viewers: 1
Package: PHP Web Application Firewall
Read this short tutorial to quickly learn how this package can help protect your site against unexpected malicious requests.
Suspicious Requests
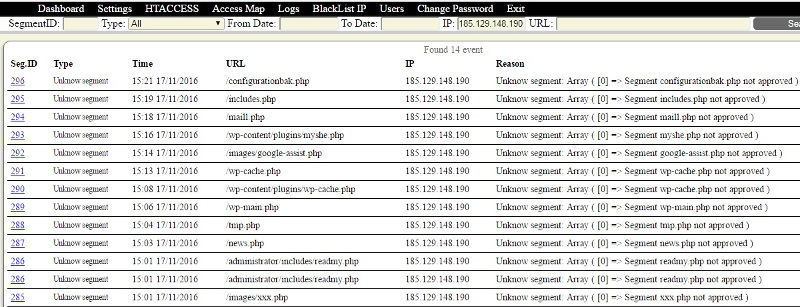
Just one week before I protected one my web site by using the Web Application Firewall package, I found strange requests coming from IP: 185.129.148.190. The whois server tells me that it comes from Latvian provider, I think maybe it is botnet.
The requests for URL segment "/wp-content/" it is for the URLs of WordPress, but my project is using Gallery2.
Searching in the logs by IP it gave me the full picture of the events:
In the access map under the segment URL I found strange variable:
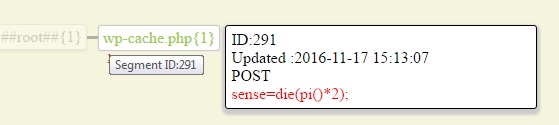
It looks like an attack. I do not know how and what it is trying to hack but since my site is protected by the PHP Web App Firewall, I should not be worried.
How to deal with suspicious requests?
What should I do after this? Of course I could add this IP to the blacklist, but it is not so important now because this request URL is not white listed any way.
Since the Web App Firewall for my site still in learning mode, as I did not yet approved all the administrative actions, I see all attack attempts as new unknown segments. It could possibly remove them, but just won't approve them!
Later after Web Application Firewall will learned the whole site structure, I will switch off the learning mode and my Access Map will be more clear, without the attack attempts, only with the real structure.
For now you can not only protect your site , but also learn newest hacker attacks attempts targeting your own site.
You need to be a registered user or login to post a comment
Login Immediately with your account on:
Comments:
1. Fantastic WAF - Tosin Omojola (2016-11-30 12:58)
I am excited to know a tool like this is available for the web... - 1 reply
Read the whole comment and replies


